Text Processing Tools and Basic System Configuration Tools in Linux
This lecture teaches you the following topics:
- An introduction to some of the most useful text-processing utilities
- Using Linux’s graphical and text-based configuration tools to manage networking, printing and date/time settings
Viewing File Contents
With less The less command is a program to view text files. Throughout our Linux system, there are many files that contain human-readable text. The less program provides a convenient way to examine them.
Why would we want to examine text files?
Because many of the files that contain system settings (called configuration files) are stored in this format and being able to read them gives us insight about how the system works. In addition, many of the actual programs that the system uses (called scripts) are stored in this format.
The less command is used like this:
![]()
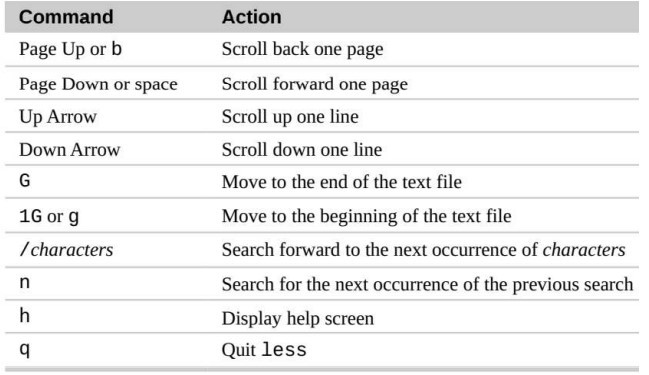
Once started, the less program allows you to scroll forward and backward through a text file.
For example, to examine the file that defines all the system’s user accounts, enter the following command:
![]()
Once the less program starts, we can view the contents of the file. If the file is longer than one page, we can scroll up and down. To exit less, press the “q” key.
The table below lists the most common keyboard commands used by less.
wc – Print Line, Word, and Byte Counts
The wc (word count) command is used to display the number of lines, words, and bytes contained in files.
For example:
![]()
In this case it prints out three numbers: lines, words, and bytes contained in Myfile.txt.
Pipelines
The ability of commands to read data from standard input and send to standard output is utilized by a shell feature called pipelines. Using the pipe operator “|” (vertical bar), the standard output of one command can be piped into the standard input of another:
For example, we can use less to display, page-by-page, the output of any command that sends its results to standard output:
![]()
Filters
Pipelines are often used to perform complex operations on data. It is possible to put several commands together into a pipeline. Frequently, the commands used this way are referred to as filters. Filters take input, change it somehow and then output it. The first one we will try is sort.
Sort
Imagine we wanted to make a combined list of all of the executable programs in /bin and /usr/bin, put them in sorted order and view it:
![]()
Since we specified two directories (/bin and /usr/bin), the output of ls would have consisted of two sorted lists, one for each directory. By including sort in our pipeline, we changed the data to produce a single, sorted list.
grep – Print Lines Matching
A Pattern grep is a powerful program used to find text patterns within files. It’s used like this:
grep pattern [file…]
When grep encounters a “pattern” in the file, it prints out the lines containing it. The patterns that grep can match can be very complex, but for now we will concentrate on simple text matches. For example, find all the files in our list of programs that had the word “zip” embedded in the name:
![]()
There are a couple of handy options for grep:
“-i” which causes grep to ignore case when performing the search (normally searches are case sensitive)
“-v” which tells grep to only print lines that do not match the pattern.
head / tail – Print First / Last Part of Files
Sometimes you don’t want all the output from a command. You may only want the first few lines or the last few lines. The head command prints the first ten lines of a file and the tail command prints the last ten lines. By default, both commands print ten lines of text, but this can be adjusted with the “-n” option:
![]()
![]()
These can be used in pipelines as well:
![]()
Networking
There are number of commands that can be used to configure and control networking including commands used to monitor networks and those used to transfer files. In this lab, we will also see the above-mentioned commands. In addition, we are going to explore the ssh program that is used to perform remote logins.
Examining and Monitoring A Network
The ping command sends a special network packet called an IMCP ECHO_REQUEST to a specified host. Most network devices receiving this packet will reply to it, allowing the network connection to be verified.
For example
![]()
After it is interrupted by pressing Ctrl-c, ping prints performance statistics. A properly performing network will exhibit zero percent packet loss. A successful “ping” will indicate that the elements of the network (its interface cards, cabling, routing, and gateways) are in generally good working order.
Traceroute
The traceroute program (some systems use the similar tracepath program instead) displays a listing of all the “hops” network traffic takes to get from the local system to a specified host. For example, to see the route taken to reach specified host, we would do this: $ traceroute
netstat
The netstat program is used to examine various network settings and statistics. Through the use of its many options, we can look at a variety of features in our network setup.
Using the “-ie” option, we can examine the network interfaces in our system:
$ netstat -ie
Using the “-r” option will display the kernel’s network routing table. This shows how the network is configured to send packets from network to network:
$ netstat -r
Activity 1:
This activity is related to file permission. Perform the following tasks
- Create a file “testfile.txt” in /test directory
- View and read the file using Less command
- Use wc command to print lines, words and bytes
- Find any text pattern in the file using grep
- Print the first 3 lines of the file using head
- Print the last 3 lines of the file using tail
Related Links to Operating System topics
Operating system Course content
- Operating System-Functions and History
- Generations of Operating System
- Functions of an Operating System
- Components of Operating System
- Types of Operating System
- Services of Operating System
- Properties of Operating System
- Processes in Operating System
- Process Scheduling in Operating System
Lab Practice Task
- Introduction to Linux Ubunto
- Installation with virtual Box
- Writing Linux Commands
- Navigation in File System and Directory Management in Ubunto using CLI
- File Handling and I/O Redirection In Ubunto
- File Access Permission in Linux
- Text Processing Tools and Basic System Configuration Tools in Linux
- Package Management in Linux
- How to manage processes in Linux
- Compiling and Executing C++ programs in Linux
- System Calls
- Introduction To Shell Programming
#Operating System complete course #Operating System past paper #Operating System-project #Computer Science all courses #operating system Problem with source code#University Past Paper #Programming language #Question paper #old paper #Operating System-Functions and History #Generations of Operating System #Functions of an Operating System #Components of Operating System #Types of Operating System #Services of Operating System #Properties of Operating System #Processes in Operating System #Process Scheduling in Operating System #Introduction to Linux Ubunto #Installation with virtual Box #Writing Linux Commands #Navigation in File System and Directory Management in Ubunto using CLI #File Handling and I/O Redirection In Ubunto #File Access Permission in Linux #Text Processing Tools and Basic System Configuration Tools in Linux #Package Management in Linux #How to manage processes in Linux #Compiling and Executing C++ programs in Linux #System Calls #Introduction To Shell Programming

